MAGNET WEEKLY CTF #9
This week begins our forensic analysis of information resident in the RAM of a Windows host when the memory was captured. The acquisition software created a .mem file that I
memory dump files in a virtual file system,
allowing the files to be viewed using Windows Explorer.
Part 1involves a conversation:
My first step was to look at the image with Volatility, so I needed to get the image info...
...then use pslist, to get an idea of which processes were running.
Of the many options, two stood out to me as potentially containing text – slack and WINWORD:
I dumped the suspect processes to files...
...ran strings | grep "password" on all of them,
and discovered this:
Success!
On to Part 2:
At first, despite my suspicions at the solution was as simple as creating an MD5 hash of my 3180.dmp file, I tried it because, after all, that is technically the file that I recovered the password from.
No go. Keep digging...
A grep of "uncrackable_password" in the MemProcFS file output found this:
That's it!
Next,
A stat of the WRD0000.tmp file was frustrating
That's the one!
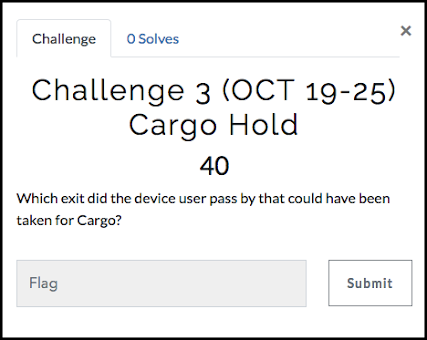
On to Part 4:
A search of the MemProcFS linked Warren to the WRD0000.tmp file:
And a look at the associated sid.txt file reveals the user ID:
One more...
And a look at the SOFTWARE registry hive in MemProcFS gives us the version number of the software that
created the document:
and that's it for another week!




























Comments
Post a Comment